
Background checks for IT recruits are standard, but as some companies discoverpainfully, potential black hats can still get hired. Threats from within have become all too commonplace, sometimes leaving companies to battle their own employees in order to achieve better security.
Yet, clamping down too fiercely can wreak havoc with employee morale and put extra strain on an already overworked IT staff. Overzealous security efforts also could put too many security barriers within an organization, reducing efficiency and increasing the number of help desk calls.
Luckily, there are ways to lock down an enterprise without locking out employees. With proper hiring practices, better training and careful forethought about security levels, companies can keep their workers honest.
Check Point
Any time an IT candidate is about to be hired, most companies should do a background check. The price of such checks has dropped dramatically since the Internet made the practice easy, and a feeling of assurance about a new employee can be priceless.
Rather than a standard check for IT potentials only, though, it may be even better to do a quick rundown on every job candidate, from accounting to data entry.
Although it might seem like overkill to double-check the resume of an administrative assistant, companies need to keep in mind that many times, it is not IT people who are misusing the corporate network or snatching data from the intranet.
“Extensive background checks are key for companies today,” said John Challenger, CEO of outplacement firm Challenger, Gray & Christmas.
He told the E-Commerce Times that checks mean not just calling references, but also checking to make sure information in a resume is accurate. There are many companies that specialize in this type of digging, and Challenger said it is worth the extra cost to outsource the work to professionals.
“If a company does an extensive amount of international trade or has technology that’s critical to its infrastructure, certainly they should be concerned about every person they hire,” he noted. “I do think companies are being more thorough about examining the people they have working on projects, but they’re still at risk during hiring.”
Training Session
Once candidates become employees, extensive training is the next step toward a more secure company. Often, new hires are told that equipment and data are owned by the organization, but that might not be enough.
Eric Ogren, Yankee Group senior analyst, told the E-Commerce Times that the weakest part of any security system is the people using it.
“What really damages companies is someone from the inside who takes a list of customer names or changes data,” he noted, adding that to prevent theft and destruction, better training must be implemented. “Far and away, education is the best thing a company can do to make itself more secure.”
This step involves making sure employees know that they are being trusted with sensitive data — and that they will be held responsible if problems occur.
“People should know how they contribute to the health of a company,” Ogren said, “and they should be made aware of how their actions affect that health.”
Software Solutions
Although educating employees can result in a definite improvement in security, it certainly does not hurt to establish some barriers between workers and data.
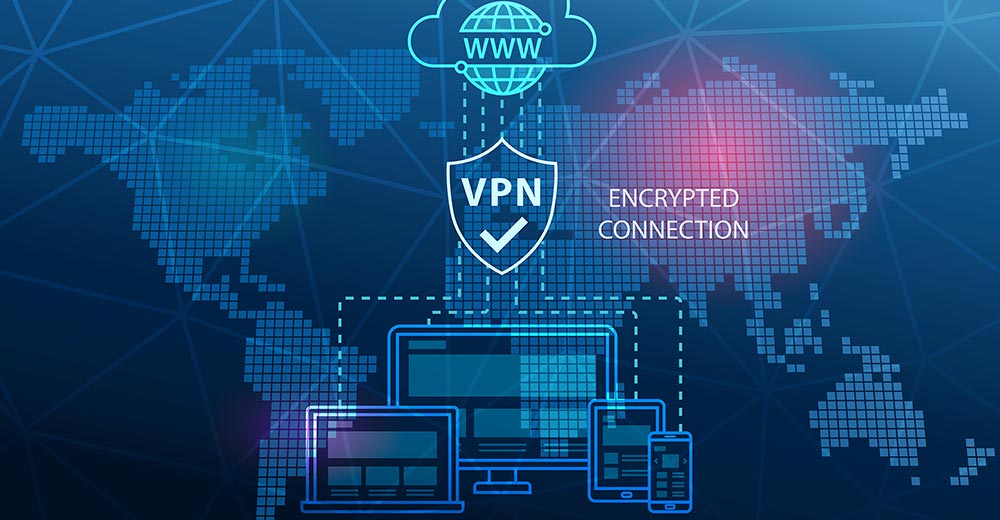
“Not all internal security breaches are intentional,” said Sweta Duseja, project marketing manager at security firm Check Point (Nasdaq: CHKP). She told the E-Commerce Times that problems often occur when someone discovers that he or she can look at another department’s data on a shared network.
“The reality of such inadvertent incidents is now dawning on a lot of companies,” she said. “They’re realizing that you used to just protect the perimeter but that now, with wireless and people working at home, the perimeter is disappearing.”
The solution, Duseja said, might lie in implementation of a layered security system that puts firewalls at different points and severely limits data access. Beyond the network level, firewalls can be erected at the application and desktop levels to give employees only the access they need.
“Some executives might think such an approach is too much,” Duseja noted. “They’d say it takes too much money or too much time, and they throw up their hands and tell IT to just do security on a large scale rather than a granular level. In my opinion, that’s pretty dangerous.”
Level Best
When it comes to granting access to data, good planning is just as crucial as employee education and use of proper security tools.
As Duseja said, “Just because I work at the same place as the person who sits down the hall doesn’t mean I should have access to their computer.”
It might be tempting — and it certainly is easy — to throw a firewall around the intranet and call it a day, but better security requires a tiered system. As Challenger noted, “A company may want to think about it the way the government thinks about security clearances.”
In other words, just because an FBI agent and a DMV clerk both work for the government does not mean they have the same level of access to information. Similarly, a company can provide different security clearance levels to different employees, even within the IT department.
Temporary clearances to access another department’s data and higher security levels for long-time employees also can help keep systems safe from inside jobs.
No security system is perfect, but it is easier to keep sensitive information safe when the bad guys are known. Realizing that the miscreants might be just a few doors down the hall is a reality check every company should pause to consider.























































Social Media
See all Social Media