
The email addresses and device IDs of more than 100,000 owners of 3G-enabled iPads have been exposed in a security breach, according to wireless provider AT&T.
Victims apparently include at least one member of the U.S. President Barack Obama’s cabinet, heads of large corporations and other prominent people.
AT&T has since shut down the feature thought to be responsible for the leak.
Cracking the iPad Owner’s Data
The breach was apparently discovered by a group of security advisers that calls itself “Goatse Security.”
Goatse obtained iPad owners’ emails through a script on AT&T’s website that was accessible over the Internet. An iPad owner would provide an ICC-ID — an identification number for the device — in an HTTP request to the site. The site would then return the email address associated with that ICC-ID number.
That gave the hackers the email addresses of iPad owners whose ICC-IDs they had identified.
An ICC-ID is an integrated circuit card identifier. It identifies a subscriber identity module (SIM) card in a mobile telephony device. Owners of these devices can change their devices by removing the SIM card from their existing device and putting it into another.
The ICC-ID includes an issuer identification number, a major industry identifier, a country code, an issuer identifier, and an individual account identification number.
Testing that information lets one know who owns the device and which country the owner is in.
Goatse’s experts managed to guess a large number of ICC-IDs by looking at known iPad 3G ICC-IDs. Some of these were in pictures of the iPad posted by owners on the Internet. The experts then wrote a PHP script to automate the harvesting of data.
Goatse reportedly shared the script with third parties and notified AT&T of the breach, though AT&T has denied it had been notified by the group. Goatse did not respond to requests for comment by press time.
Reaching for the Sky
Some of the iPad’s earliest adopters include high-profile individuals in positions of power who presumably would want their personal email addresses kept private. Victims of the breach include White House Chief of Staff Rahm Emmanuel, as well as staffers in the U.S. Senate and other major government departments, according to a post on the blog Gawker.
Others apparently work for the Defense Advanced Research Projects Agency (DARPA) and other major branches of the United States’ armed services. Other victims include top executives of The New York Times and Dow Jones; high-level staff at Google, Amazon and Microsoft; and staff at financial industry companies like Goldman Sachs and JP Morgan.
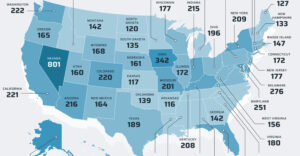
There are at least 114,000 victims in the United States alone, Gawker reported.
Could Apple be partly responsible for the breach because it requires iPad owners to provide their email addresses in order to get service?
No, David Harley, director of malware intelligence at ESET, told the E-Commerce Times. “AT&T is hardly a mom-and-pop operation, and it wasn’t unreasonable for Apple to expect professionalism and expertise from the partnership with AT&T.”
Apple did not respond to requests for comment by press time.
AT&T Clamps Down
AT&T has shut off the feature that provided iPad owners’ email addresses in response to HTTP requests.
“We have essentially turned off the feature that provided the email addresses,” AT&T spokesperson Mark Siegel told the E-Commerce Times.
He disputed reports that Goatse had notified AT&T of the breach.
“The person or group who discovered this gap did not contact AT&T,” Siegel said. “AT&T was informed by a business customer on Monday of the potential exposure of their iPad ICC-IDs.”
AT&T is still investigating the breach and will inform all customers whose email addresses and ICC-IDs may have been breached.
All Sizzle, No Steak?
The breach is a tempest in a teacup, Carl Howe, director of anywhere research at the Yankee Group, told the E-Commerce Times.
“People can find out your email address. Who knew?” Howe said. “Most people are sending their email addresses to hundreds of people every day and don’t worry about security.”
“Activation and registration that requires an email address is very common in the software industry,” ESET’s Harley pointed out. “Its use in terms of the iPad is entirely consistent with Apple’s security model which is, in many ways, very effective.”
Hackers won’t get much out of the information gleaned from the attack, Howe said.
“You can’t do anything with the iPad serial number, it’s not terribly useful to anyone else other than A&T,” Howe remarked. “The hackers have the serial numbers of iPads and their owners’ email addresses, and that’s all,” he said.
“It’s a design flaw, certainly, but its impact is mostly in terms of bad public relations,” ESET’s Harley said. “It’s mostly AT&T’s bad luck that it was picked up by a group that saw an easy way to get some publicity. It seems to me that the risk has been somewhat overstated.”
The real impact of the hack will be inconvenience for iPad owners, Howe said.
“AT&T were trying to make it easier to buy services by automatically filling in users’ email addresses when they ordered, say, an iPad app,” Howe explained. “Now you’ll have to type in your email address when you order something for the iPad on AT&T’s website.”





























































































This is straight from Carl Howe’s bio:
"Carl Howe is a director for Yankee Group’s Anywhere Consumer research group"
Maybe you’ve just taken his comments out of context, but if not, next time contact a security expert for any security related comments.
"The breach is a tempest in a teacup, Carl Howe, director of anywhere research at the Yankee Group, told the E-Commerce Times"
We are talking about at least 114,000 emails of people. You could get good money for such a list which wouldn’t be the case if this data was easy to access without this leak. If you went up to the CEO or other higher ups on that list and asked for their email do you think they would just give it to you? No, they give it to they people they trust or want to have a relationship of some kind with. Having these emails compromised in a way where anybody who wanted to could see them is huge!
"You can’t do anything with the iPad serial number"
The article has already showed how this can be linked to an actual user via a photo. You have already seen what little info it took for the group to expose other data.
"The hackers have the serial numbers of iPads and their owners’ email addresses, and that’s all,"
The article identifies other information which is exposed.
"It’s mostly AT&T’s bad luck that it was picked up by a group that saw an easy way to get some publicity. It seems to me that the risk has been somewhat overstated."
WRONG! Part of my job involves programming. It’s very bad programming (or management decisions) that lead to this security issue. You do no expose private information without requiring some good form of authentication before hand, it’s that simple. This was really bad code that allowed this to happen.