Digital Forensics Corporation is battling to protect and educate the public about a rapidly growing trend in cybercrime dubbed sextortion, where online predators target teens and young adults with threats to expose sensitive personal photos.
The extortionists disguise their identity on social media platforms, claiming to have a revealing picture or video that they will share unless the victim sends more images, pays money, or performs lewd acts. These attacks claim the lives of many teens and cause immense anxiety, depression, and financial loss to thousands.
Financial sextortion is on the rise, noted the U.S. Department of Homeland Security’s webpage on sextortion, which shares growing concerns by the National Center for Missing and Exploited Children (NCMEC) about the dangers to youngsters victimized by such cyberattacks. A recent analysis by that agency disclosed that as many as 79% of predators seek money rather than additional sexual imagery.
What makes this type of cyberattack different from other extortion crimes is its connection to hacking, noted Digital Forensics’ Public Relations Manager and former Digital Investigator Kenneth Kuglin. The perpetrator has already gained access to sexual material either provided by or stolen from the victim.
“Traditional sextortion occurs when a victim is threatened or blackmailed into providing more sexual imagery. The predator threatens to share the nude or sexual images with the public,” he told TechNewsWorld. A far more common type nowadays is financial sextortion. A predator demands money or gift cards in exchange for keeping the sexual content private.
Sextortion More Common Than You’d Think
Kuglin balked at the stereotypical use of the word “attacks” when associated with sextortion. That word is not the best one to describe the techniques that criminals use.
“Rather than picturing a hacker who is able to access your cloud and gain access to private photos, the overwhelming majority of sextortion cases involve social engineering,” he countered. “The perpetrator manipulates victims into sending the images voluntarily, through techniques of catfishing, posing as someone the victim would like to be intimate with, and then afterward revealing their intentions to blackmail.”
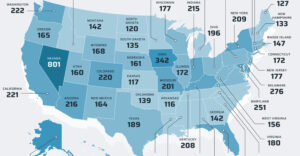
Law enforcement agencies are seeing an increasing surge in the prevalence of sextortion since the 2020 global pandemic. According to the FBI, more than 7,000 reports of sextortion happened in 2022.
Thorn, an organization focused on fighting child sexual abuse, conducted a survey in 2017 that revealed 33% of sextortion victims in the study had not told anyone due to shame or embarrassment.
“Digital Forensics saw a massive surge in cases related to sextortion since 2020. Our digital analyst team reported that at least 70% of the cases they handled were sextortion related in 2022,” offered Kuglin.
Effective Modus Operandi
Cybercriminals typically operate online through various social media platforms, dating apps, and messaging services to target vulnerable individuals, such as teenagers or young adults, he explained.
“Very often, we see a pattern wherein these criminals contact a victim on one platform, then ask them to move to a second or even third that uses encrypted messaging, which makes it more difficult to track their crimes,” said Kuglin.
While sextortionists can operate independently, they often work within an organized group or network that oversees their activities. These organizations are located in different parts of the world, making it challenging for law enforcement agencies to track them down and bring them to justice.
“The employers of these sextortion empires provide their employees with resources such as a laptop and media to use to create false profiles, and in return, will take a cut of the profits that the employees acquire through sextortion,” he observed.
Skilled Con Artists
Sextortionists use various tactics to target their victims and obtain sexually explicit images or videos. The methods are particularly effective in entrapping unaware youngsters.
One tactic is to post personal ads on platforms such as Craigslist or Reddit, where they pretend to seek intimacy to coerce victims to respond. A similar ploy involves creating fake profiles on online dating sites such as Tinder or Ashley Madison.
Another method employed by sex cybercriminals is to reach out directly to potential victims on social media such as Instagram, Facebook, or Snapchat with fake profiles designed to match a target’s erotic interests.
With targeted potential victims in sight, sextortionists send unsolicited nude or explicit content to their targets via private messaging. In certain instances, the criminals may immediately threaten a target’s friends or family in an attempt to gain sexual material without any prior rapport with the potential victim.
“Pornographic content is associated with diminished gray matter in the prefrontal cortex compared to baseline, and this tactic is intended to decrease the decision-making ability of a target,” noted Kuglin.
Leveraging the Outcome
The goal is to acquire sexually explicit material from a victim. Then the perp uses it as leverage to coerce the victim into providing more explicit material or complying with financial demands.
Threatening to share the images with the victim’s friends and family or posting it publicly online is a common threat. Sextortionists sometimes create websites dedicated to shaming a victim.
In order to increase the pressure on the victim, sextortionists often send screenshots of the victim’s friends list or other personal information to demonstrate their access to the victim’s social network.
“This can be an incredibly distressing experience, as it not only exposes their intimate material but also puts their reputation and personal relationships at risk,” said Kuglin.
Local Law Enforcement Often Ill-Prepared
An unfortunate reality of the current predicament is that most local police precincts and municipalities have little training or equipment to properly track or engage with suspects in blackmail reports, considering the timely nature of such cases, noted Kuglin.
Since most cases of sextortion originate outside the United States, there is often very little local police and authorities can do to help victims.
“That said, it is still important to start a trail of documentation as reports of sextortion can help future legislation,” urged Kuglin.
Victims should file a report with local authorities and the FBI’s Internet Crime Complaint Center (IC3). He counseled that these steps would help document the gravity of this online epidemic.
Help and Advice for Sextortion Victims
If a minor is involved, contact the National Center for Missing & Exploited Children at 1-800-THE-LOST (1-800-843-5678). Take It Down is a free service offered by the NCMEC that can help to remove or stop the online sharing of sexually explicit images or videos taken of victims before they were 18 years old.
Above all, victims should not comply with the blackmailer’s demands, according to Kuglin. Once a sextortionist receives funds from a target, their threats will always increase in volume as they now have certainty of their influence over the victim.
Another response strategy is to reach out to a close friend or family member to help the victim cope with the emotional strain of this experience. He suggested contacting his company’s team of specialists who have years of experience in case resolution with these types of criminals.
“When a victim comes to us with a case of sextortion, the specialist assigned to a case will work quickly to assess the situation and develop a plan of action,” he offered. This involves gathering evidence, such as chat logs or emails, and taking over correspondence with the criminal by impersonating the client and gathering evidence against the criminal.
“Our team also works with certain overseas law enforcement teams and other authorities to ensure that the perpetrator deletes our clients’ material,” said Kuglin.
Digital Forensics handles the immediate threat and continues monitoring clients’ accounts to ensure they are always protected if they wish. The company informs and educates clients so that it does not happen again.
“Most importantly, we give them a chance to talk about what happened in a judgment-free place, which is huge for many people,” he noted.
How To Avoid Sextortion
The most effective way to avoid sextortion is obvious, quipped Kuglin. Never share nude or intimate photos online, especially with strangers, and better yet, not at all.
Recognize the red flags and manipulation techniques that sextortionists may use to try and get you to violate this commitment. Kuglin recommends these online best practices:
- Be cautious when interacting with strangers online: Avoid sharing personal information or explicit material, especially with anyone you don’t know and trust.
- Use privacy settings on social media: Adjust the privacy settings on your social media accounts to limit who can see your posts and personal information.
- Do not move conversations to other platforms: Avoid moving conversations to a more private platform, as this can make it easier for sextortionists to exert control and pressure.
- Report suspicious activity: If someone makes threats or demands or behaves suspiciously, report it to the relevant authorities or the platform you are using.
“It is important to note that these are just a few examples of the tactics that sextortionists may use. They are constantly evolving their methods to stay ahead of law enforcement and other authorities, making it crucial for individuals to remain vigilant and cautious when interacting with people online, Kuglin concluded.

























































Social Media
See all Social Media