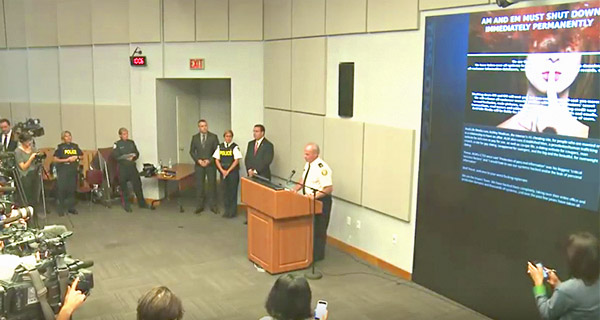
The Toronto Police Service on Monday held a press conference to report on the progress of Project Unicorn, the official investigation into the hack attack on Ashley Madison, an adultery-promoting website.
The Toronto police are working closely with the U.S. Department of Homeland Security, the Royal Canadian Mounted Police, the U.S. Federal Bureau of Investigation, and the Ministry of the Attorney General’s criminal law office in carrying out the investigation.
They have received full cooperation from other law enforcement groups around the world, Toronto Police Service Acting Staff Superintendent Bryce Evans told reporters.
Fallout From the Crime
“The ripple effect has and will continue to have a long-term social and economic impact, and [the hackers] have already sparked spinoffs of crimes and further victimization,” Evans said. “We have two unconfirmed reports of suicides that are associated, because of the leak of Ashley Madison’s customers’ profiles.”
Criminals are running scams claiming to provide access to the leaked websites, but people clicking on the links they provide are exposed to adware, malware, spyware and viruses, Evans warned.
Websites that offer to erase members’ profiles from the published Ashley Madison database also are a scam, because the information has been downloaded to multiple sites, Evans said. “Nobody is going to be able to erase that information.”
There are confirmed cases of criminals trying to extort Ashley Madison members by threatening to tell others their information has been published unless they pay a fee in bitcoins equivalent to US$225.
Data Dumped
Some credit card information of Ashley Madison members has been released, Evans said, including the card holders’ names, billing details, home addresses, transactions and records.
However, only the last four digits on the cards were released.
Ashley Madison members should review their credit card records and take appropriate measures to protect their accounts, Evans advised.
Victims of extortion and other crimes relating to the data leak should file reports with law enforcement.
Other Investigations, Lawsuits
There are about 15,000 accounts tied to government or U.S. military email addresses are in the Ashley Madison database, which has sparked investigations by various state, local and city governments, as well as by the Pentagon.
A number of those email addresses are associated with several agencies and city governments in Alabama, whose residents spent more than those of any other state, per capita, on Ashley Madison. Email addresses also have been tied to public agencies throughout southern California, the State of Illinois and local authorities there, and the city of Indianapolis.
Meanwhile, at least five lawsuits seeking class-action status reportedly have been filed against Ashley Madison and Avid Life Media, seeking damages totaling more than $500 million.
Four are federal lawsuits.
Watch Out, Impact Team!
TPS’ Evans issued a harsh warning to Team Impact, the hackers behind the Ashley Madison breach.
“I want to make it very clear to you: Your actions are illegal and will not be tolerated,” Evans said. “This is your wake-up call.”
Further, Evans urged other members of the hacking community to reach out to law enforcement if they had I information, saying the Impact Team had crossed the line.
He thanked the open source community for its assistance.
Avid Life Media, the parent company of Ashley Madison, has offered a CA$500,000 reward for information leading to the identification, arrest and prosecution of those responsible for the hack.
Not Your Average Breach
The average data breach sees personal data and credit card information stolen, resulting in financial loss and identity theft, and considerable embarrassment to the company whose servers were hit.
In the Ashley Madison case, the embarrassment accrues to the site’s members, not the company. The social ramifications of the hack are unprecedented.
Members are being blackmailed and targeted by extortionists. Some may have had their identities stolen. Marriages are being affected, people may lose their jobs or have their careers impeded.
“The Ashley Madison breach is notable because of the nature of their business,” said Tim Erlin, director of IT security and risk strategy at Tripwire.
“Part of the value proposition for Ashley Madison was identity protection of a sort,” he told the E-Commerce Times. “The breach made that which was secret public — and in doing so, put a large number of individuals across various demographics in potentially difficult and dangerous positions.”
The impact of the hack will continue to be felt over a long period of time, Erlin predicted.
More Than Data
Shame and social condemnation will be felt not only by Ashley Madison site members but also by their families and friends.
“It’s not very often that a company data breach can potentially break up marriages, lead to the blackmailing of its users, and cause suicides,” mused Nathan Sorrentino, marketing manager at Stealthbits.
“The very nature of what Ashley Madison was in business to do is driving such widespread interest,” said Suni Munshani, CEO of Protegrity.
“Add in a touch of blackmail, corporate espionage, celebrity, ethical and moral debates, as well as anecdotal evidence of breakups, divorces and even worse — and you have all the makings of a story that won’t go away any time soon,” he told the E-Commerce Times.
Breach of Trust
There’s a possibility that the Ashley Madison hack could change how consumers approach the Web in the future.
“Trust can be a very hard thing for a business to earn,” Stealthbits’ Sorrentino told the E-Commerce Times, adding that sites like Ashley Madison “should expect to be put under the microscope by users.”
Consumers engaged in private online activities might become more cautious, suggested Jeff Hill, channel manager for Stealthbits. “Would you rather the bad guys have stolen the credit card number you used to buy lawn furniture at Target, or … Ashley Madison?”
Consumers might not be so alert when it comes to other sites, though.
“While I would welcome a consumer revolt demanding that the businesses that collect and store their sensitive data do a better job of protecting it, I don’t see much evidence that this will happen any time soon,” Munshani said.
Corporations May Just Chug Along
Cybercrooks with an ax to grind — which the Impact Team apparently had — might be “emboldened to take action and launch copycat attacks,” Tripwire’s Erlin said.
“The stakes have been immeasurably and irreparably raised for infosec professionals,” he pointed out. “There was a time when assuring that credit card numbers … were secure was the holy grail of infosec.”
Hackers motivated by a sense of morality, however warped, are more difficult to tackle.
There’s an “endless list of motivations beyond simple greed,” Stealthbits’ Hill told the E-Commerce Times, which “makes securing sensitive information in this environment exponentially more challenging than just a few years ago.”






















































Social Media
See all Social Media