Attackers for months have been using eBay listings to redirect visitors to password-harvesting scam sites, the BBC reported. They use cross-site scripting to hijack eBay shoppers and trick them into handing over personal data.
Smartphones, televisions, hot tubs and clothing are among the items supposedly for sale in listings infected with malicious Javascript code. When users click on the listings, the code redirects them through a series of other websites to a page requesting their eBay log-in and password.
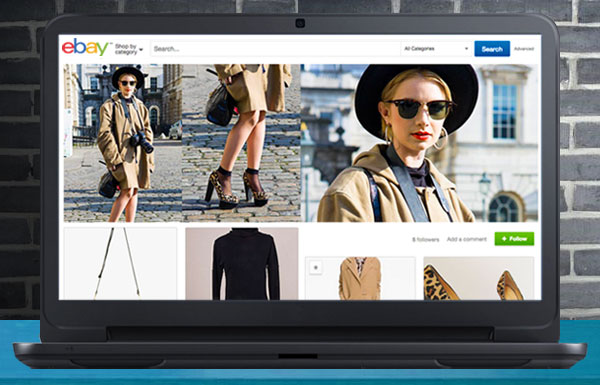
This video, taken by a user, demonstrates the exploit in action:
eBay has been slow in responding to security professionals’ calls to remove the fake listings, said the BBC, which on Monday reported finding more than 100 listings affected by the exploit.
Nothing New
“Cross-site scripting, carried out by malicious individuals, is an issue affecting sites across the Internet,” eBay spokesperson Ryan Moore told the E-Commerce Times. “This is not a new type of vulnerability on sites such as eBay.”
The problem is made possible by the fact that eBay allows sellers to use active content like Javascript and Flash to make their listings on the site more attractive, Moore said. “However, we are aware that active content may also be used in abusive ways.”
Cross-site scripting is not allowed on eBay, however, and “we have a range of security features designed to detect and then remove listings containing malicious code,” he noted, adding that unauthorized account usage currently is at an all all-time low on the site.
Still, “the criminals behind cross-site scripting and phishing activity intentionally adapt their code and tactics to try to stay ahead of the most sophisticated security systems,” Moore pointed out.
Easy Money
“eBay is apparently suffering from the losing end of a common ‘risk versus convenience’ scenario,” Mark Stanislav, a security project manager with Duo Security, told the E-Commerce Times.
“By providing the ability for users to add Javascript and Flash content to improve buyer experiences, they’ve also allowed attackers to craft code which can manipulate consumer browsers to benefit criminals,” he said.
These attacks are similar to recent attacks against ad networks that have allowed Javascript to be embedded, noted Ken Westin, a security analyst with Tripwire.
Other very similar exploits can do even more damage, Westin told the E-Commerce Times.
“If the attackers target vulnerable browsers and systems with this kind of exploit, it can lead to instant compromise of the system,” he explained.
“Since online buyers have become accustomed to interactive content, we’ll probably continue to see more of these kinds of attacks; they are lucrative and relatively easy for attackers to implement,” Westin observed.
Tough Problem
“eBay is a community of sellers and buyers, and it’s vital to eBay’s business model to provide merchants with the ability to draw in more customers through the use of customized, interactive Web pages and content,” Tim Erlin, director of IT security and risk strategy with Tripwire, told the E-Commerce Times.
“This is a tough problem to stay on top of, but the success of eBay’s model depends on doing just that,” he added. “If consumers or merchants flee to alternatives because of a real or perceived lack of responsiveness from eBay, they lose revenue.”
While many Internet users readily accept Javascript in Web pages, largely on the strength of their trust in the site, that’s no longer the case with Javascript in emails, “because scripts delivered by email could have come from anywhere, and probably did,” Paul Ducklin, a senior security advisor at Sophos, told the E-Commerce Times.
One step eBay could consider taking is a per-user option to strip scripts out, he suggested. “Then we could shift the argument to whether to have that option on or off by default.”
Security Vigilance
In the meantime, users should be cautious, warned Duo Security’s Stanislav.
“It’s very hard for users to know they are being duped into doing something wrong online,” he explained. “Paying attention to what your browser address bar says is a very low-tech, high-value means to ensure that if you think you’re using eBay.com that you’re actually on that website when logging in.”
On SSL-enabled sites, “pay attention that you’re on a site with a valid certificate through the coloring/icons browsers provide to denote that fact,” he suggested.
“Users can help mitigate the effectiveness of these criminal ploys by utilizing the two-factor authentication provided by the service,” Stanislav recommended, “and also applicable for PayPal.”












































As a past eBay buyer, I want to express my concern for their disregard for their millions of members by not letting us know they are compromised. The lack of an ongoing investigation to clarify that they are doing all they can to protect users. I have since stopped buying on their site. I’m very upset for their disregard to now exposing all our names, birthdates, addresses, and all the other demographics. I read the other day a story Joe Ducey published on the news about eBay sellers STILL being scammed (December, 2014). In this case they said they were scammed and the emails that their diamond jewelry bought was in fact not bought. This person was not a regular seller and the email said to ship now. Here’s where it gets really concerning. If eBay did not sell them and it was a bogus email, then why did they send them an invoice for selling the items? I thought they didn’t know anything about it? This in addition to many other articles I have read discourages me and the disrespect is overwhelming.
People who aren’t sure if their password is secure should use PasswordTurtle.com! PasswordTurtle makes passwords from normal english phrases so the passwords are easy to remember and secure. I use them whenever I make a new online account.